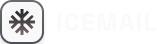
DMARC Failures: Using Reports to Identify Issues
Use DMARC aggregate and forensic reports to identify SPF/DKIM alignment, DNS, and third-party issues and fix deliverability.
DMARC (Domain-based Message Authentication, Reporting, and Conformance) is essential for protecting your domain from phishing and spoofing attacks. However, misconfigurations and alignment issues can cause legitimate emails to fail DMARC checks, leading to blocked or spammed messages. This disrupts email campaigns and damages sender reputation, especially with major providers like Google, Yahoo, and Microsoft enforcing stricter DMARC compliance since 2024-2025.
Key Takeaways:
- Common DMARC Failures: Misalignment between the "From" domain and SPF/DKIM, DNS errors, and third-party service misconfigurations.
- DMARC Reports: Use aggregate and forensic reports to identify unauthorized senders, misalignments, and configuration issues.
- Fixing Issues: Adjust SPF/DKIM settings, resolve DNS errors, and align third-party services with your domain.
- Automation Tools: Platforms like Icemail.ai simplify DMARC setup, offer actionable insights, and improve email deliverability.
DMARC failures are often caused by alignment problems or misconfigured DNS records. The solution lies in analyzing DMARC reports, fixing alignment issues, and gradually enforcing stricter policies. Tools like Icemail.ai can streamline this process, saving time and ensuring better results.
Why is DMARC failing? How to fix DMARC Failure report? What is a DMARC Failure Report?
sbb-itb-1cb964a
Common Reasons for DMARC Failures
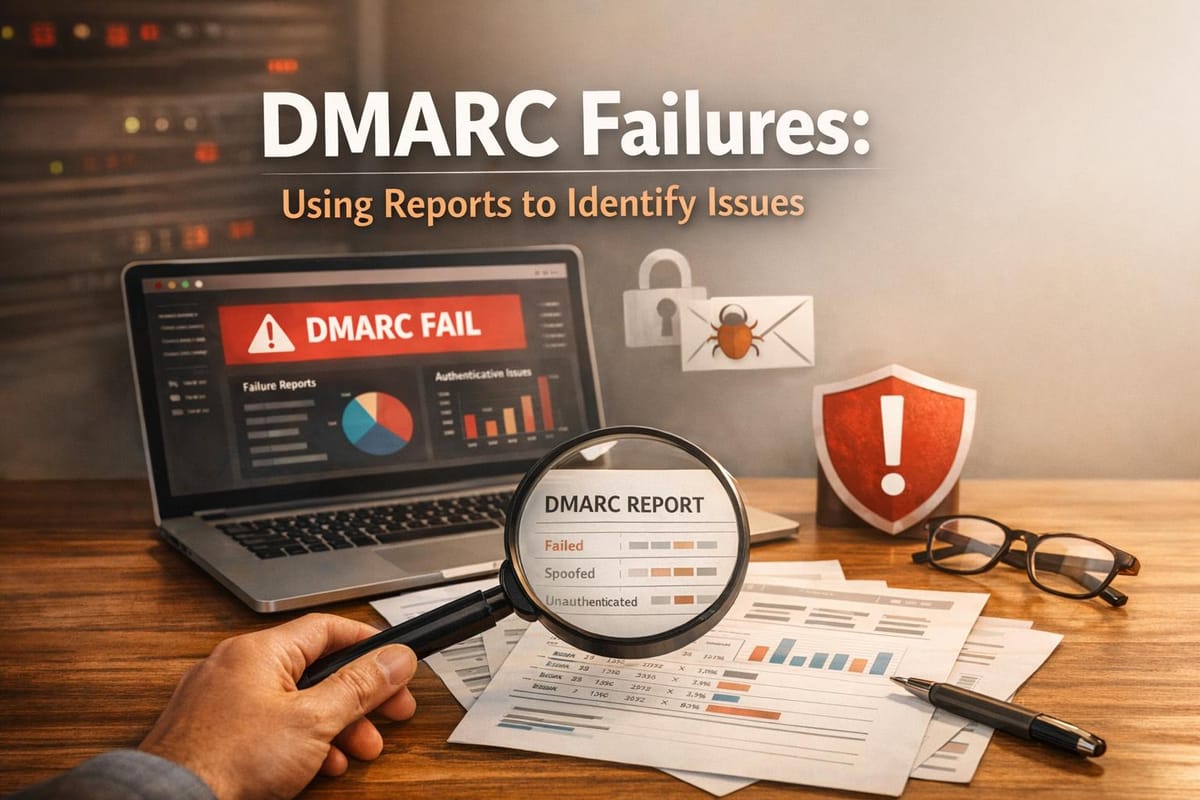
Common DMARC Failure Causes and Statistics
DMARC failures generally arise from three main issues: SPF/DKIM alignment errors, DNS configuration mistakes, and misconfigured third-party services.
A study focusing on Gmail's DMARC failures found that 62% were due to alignment problems with third-party platforms, 21% resulted from exceeding SPF lookup limits, and 11% were caused by expired or incorrectly published DKIM keys. Let’s dive into these issues to better understand how to use DMARC reports for improving email deliverability.
SPF and DKIM Alignment Problems
Alignment is often misunderstood when it comes to DMARC. Even if SPF and DKIM pass, a mismatch between the authenticated domain and the "From" domain will still cause a DMARC failure.
- SPF alignment fails when the Return-Path domain (used by SPF) doesn’t match your "From" domain.
- DKIM alignment fails if the
d=tag in the DKIM signature points to a domain different from the one in your "From" header.
DMARC offers two alignment modes:
- Relaxed: Allows subdomains to match the parent domain.
- Strict: Requires an exact match.
For example, if you use strict alignment and your DMARC policy is set on example.com, emails sent from marketing.example.com will fail alignment - even if they’re legitimate.
To diagnose alignment issues, check the <policy_evaluated> section of your DMARC reports. If you see <spf>fail</spf> or <dkim>fail</dkim> but the <auth_results> section shows "pass", the problem lies with alignment, not authentication. The <header_from> field indicates the visible domain, while <auth_results> shows the domain that was authenticated.
DMARC Policy Configuration Mistakes
Errors in your DNS records can quietly undermine DMARC effectiveness. Common pitfalls include:
- Missing the
v=DMARC1tag. - Using invalid policy values (e.g.,
p=blockinstead ofnone,quarantine, orreject). - Forgetting the
mailto:prefix in reporting URIs.
Another frequent issue is publishing multiple DMARC records for a single domain. This creates ambiguity, leading receivers to ignore your policy altogether. A February 2026 analysis of 5.5 million domains revealed that 69.6% lacked a DMARC record entirely, and only 6.0% enforced a p=reject policy.
"The most common mistake we see during DMARC setup is jumping straight to p=reject without monitoring first. Start at p=none, analyze your reports for at least a full quarter - you need to catch monthly, quarterly, and annual email senders that only fire periodically."
- Vasile Diaconu, Operations Lead, DuoCircle
Another critical misstep involves the SPF 10-DNS-lookup limit. Each include mechanism in your SPF record counts toward this limit, and exceeding it triggers a PermError, causing SPF to fail entirely. The same February 2026 study found that 2.7% of domains exceeded this limit - approximately 148,655 domains.
Subdomains can also cause issues. By default, they inherit the DMARC policy of the root domain. If your root domain enforces p=reject and you haven’t configured specific subdomains that send mail, those emails will be blocked.
Third-Party Email Service Issues
Third-party email platforms are a major source of DMARC failures. These platforms often authenticate emails using their own domains - like mcsv.net, hubspotemail.net, or zendesk.com - which don’t align with your "From" domain.
These failures often result from teams adopting new tools without involving IT to configure proper SPF and DKIM records. Your DMARC reports can help identify unauthorized senders by examining the <source_ip> field, which can be traced back using reverse DNS lookups.
The SPF lookup limit becomes particularly challenging when using multiple third-party services. Each service requires its own include mechanism, and adding several platforms can easily push you beyond the 10-lookup limit, causing SPF checks to fail.
To pinpoint third-party issues in your DMARC reports, check the <auth_results> section. If you see d=klaviyomail.com while your "From" header lists example.com, this indicates an alignment problem. Resolving this often requires setting up custom DKIM configurations for the platform in question.
How to Read and Analyze DMARC Reports
Once you've identified DMARC failures, the next step is understanding the reports to address policy issues and improve email deliverability. After you publish a DMARC record, reports typically start arriving within 24–48 hours. Most mailbox providers send these reports daily, and they come as XML files that might seem complicated but are full of useful insights.
There are two main types of reports: aggregate reports (RUA) and forensic reports (RUF). Aggregate reports offer daily summaries of all emails claiming to be from your domain, including details like source IPs, message counts, and authentication results. Forensic reports, on the other hand, provide real-time alerts for individual emails that fail DMARC, including headers and reasons for failure.
Understanding DMARC Aggregate Reports
Aggregate reports are daily XML summaries sent by receiving servers like Gmail, Yahoo, and Outlook. Although they don't include the actual email content, they provide metadata about authentication attempts.
Each report has three key sections:
- Report Metadata: This identifies the reporting organization (e.g., google.com), the report ID, and the 24-hour period covered.
- Policy Published: This section shows how the receiving server interpreted your DMARC record, including your policy (none, quarantine, or reject) and alignment settings.
- Record Rows: These rows detail each sending server's IP, the number of messages sent, and the DMARC verdict.
To troubleshoot, compare the auth_results (SPF and DKIM outcomes) with policy_evaluated (the DMARC alignment result). For example, a message might pass SPF or DKIM but still fail DMARC if domains aren't aligned.
The header_from field is crucial - it shows the visible domain in the "From" header. DMARC checks whether this domain aligns with the envelope_from (used for SPF) or the dkim_domain (used for DKIM). If they don't match, alignment fails, even if authentication passes.
| Field | What It Reveals | Why It Matters for Troubleshooting |
|---|---|---|
| source_ip | IP address of the sending server | Identifies unauthorized senders or missing ESP IPs |
| count | Number of messages sent from that IP | Helps prioritize high-volume senders |
| header_from | Domain in the visible "From" header | Establishes the reference domain for SPF and DKIM alignment |
| disposition | Action taken (none, quarantine, reject) | Indicates whether your DMARC policy is being enforced correctly |
| envelope_from | Domain used for SPF evaluation | Mismatches with header_from suggest SPF alignment issues |
| dkim_domain | Domain used for DKIM signing (d=) | Mismatches with header_from suggest DKIM alignment issues |
You can use reverse DNS lookups on the source_ip field to check if the IP belongs to your approved email service provider, your mail server, or an unauthorized source. For instance, if you see a high message count from an IP linked to mcsv.net, it likely means Mailchimp is sending on your behalf and needs proper configuration.
While aggregate reports show overall trends, forensic reports focus on individual failures.
Reading Forensic Reports
Forensic reports, also called failure reports or RUF reports, are sent in real time to the email address specified in the ruf tag of your DMARC record. Unlike aggregate reports, they provide detailed notifications about individual messages that fail DMARC.
These reports use the plain-text Abuse Feedback Reporting Format (AFRF) to detail failures. Since they may include sensitive information - like email headers, subject lines, and recipient addresses - major providers like Gmail often don't send them due to privacy concerns.
"Forensic reports are your early warning system. They help you spot spoofing attempts quickly when unauthorized servers try to use your domain." - Jack Zagorski, DMARCeye
When analyzing a forensic report, start with the Source-IP field. If the IP isn't linked to a legitimate service or vendor, it could indicate a spoofing attempt. Next, review the Authentication-Results header to see the SPF, DKIM, and DMARC status (e.g., spf=fail or dkim=none). Comparing the Original-Mail-From (envelope-from) and Header-From fields can highlight alignment problems, especially with third-party services.
To generate more detailed reports, include the fo=1 tag in your DMARC record. This ensures a forensic report is triggered if either SPF or DKIM fails, not just when both fail. It's a good idea to send these reports to a dedicated mailbox, like [email protected], to manage their volume and sensitive content.
Important Metrics to Monitor in DMARC Reports
Keeping an eye on key metrics can help you catch issues like configuration problems, unauthorized senders, or alignment errors before they affect email deliverability. Focus on these indicators:
- Pass/Fail Percentages and Policy Enforcement Rates: Use the
dispositionfield to track how often emails pass DMARC and whether your policy is being applied consistently. A sudden drop in pass rates might mean a new service is sending emails without proper setup. - Source IP Diversity: A spike in unique sending IPs could signal unauthorized domain use. Use reverse DNS lookups (e.g.,
dig -x [IP]) or WHOIS data to verify if failing IPs belong to trusted third-party services like SendGrid or Mailchimp. - Alignment Failures: If a legitimate service shows "SPF pass" but "DMARC fail", it's likely an alignment issue. Setting up a custom Return-Path domain can help ensure proper alignment with your "From" header.
During the initial rollout of DMARC, reviewing reports weekly is recommended. Once you're using a strict p=reject policy, monthly reviews should suffice.
"Without reviewing these reports, it's impossible to know whether your DMARC setup is actually doing its job." - Jack Zagorski, DMARCeye
To manage reports effectively, use a dedicated mailbox like [email protected]. For high-volume domains, weekly reviews are ideal, while smaller setups can stick to monthly checks to stay on top of unauthorized senders or configuration issues.
Fixing DMARC Failures Based on Report Data
Once you've identified DMARC failures, the next step is to address alignment and configuration issues. These failures often arise from misalignment or configuration errors, both of which can be resolved by making changes to your DNS records and email service settings.
"Alignment issues - not missing records - are the leading cause of failure." - Validity
Start by examining if your reports show "pass" in auth_results but "fail" in policy_evaluated. This indicates that SPF or DKIM is functioning but doesn't align with the "From" header domain - a classic alignment issue. Focus on high-volume unknown IPs first. For instance, a third-party ESP sending 10,000 emails daily should be addressed immediately, while low-volume forwarding issues can be resolved later. Below, we'll dive into specific fixes and how to interpret report data to resolve these problems.
Aligning SPF, DKIM, and DMARC Policies
Alignment issues are a common finding in DMARC reports. To resolve them, ensure the "From" header domain matches the SPF Return-Path or the DKIM d= tag. For example, if your ESP uses its domain (e.g., bounces.sendgrid.net for SendGrid), SPF might pass but fail DMARC alignment.
- Fixing SPF alignment: Configure a custom Return-Path with your ESP. For example, if you're using Mailchimp, you could set up a subdomain like
mail.yourdomain.comand update your DNS records accordingly. This ensures that the Return-Path domain aligns with your "From" header. - Fixing DKIM alignment: Adjust your ESP to sign emails with your domain instead of theirs. Many services provide this option as "Custom DKIM" or "Authenticated Domain." For example, SendGrid requires adding two CNAME records to your DNS so emails are signed with
d=yourdomain.cominstead ofd=sendgrid.net.
If you must choose between SPF and DKIM fixes, prioritize DKIM. Unlike SPF, DKIM signatures survive email forwarding because they are embedded in the email itself. SPF, on the other hand, often breaks when forwarding servers use a different IP address.
For Relaxed alignment (aspf=r or adkim=r), subdomains like mail.example.com will align with example.com. However, Strict alignment (aspf=s or adkim=s) requires an exact domain match. Most organizations should opt for Relaxed alignment to avoid disrupting legitimate mail from subdomains.
| Service | SPF Include Mechanism | DKIM Setup Requirement |
|---|---|---|
| Mailchimp | include:servers.mcsv.net |
3 CNAME selectors (k1, k2, k3) |
| SendGrid | include:sendgrid.net |
Authenticated Domain (2 CNAMEs) |
| Amazon SES | include:amazonses.com |
Easy DKIM (3 CNAME records) |
| HubSpot | include:_spf.hubspotemail.net |
2 DKIM CNAME records |
| Salesforce | include:exacttarget.com |
Custom sender profile |
Fixing Configuration Errors
Beyond alignment, configuration errors in DNS records can also cause DMARC failures. A common issue is exceeding the SPF 10-DNS-lookup limit. As of February 2026, 4.8% of SPF-enabled domains - over 148,000 - exceed this limit, rendering their SPF authentication ineffective. Each include: directive in your SPF record counts as one lookup, and nested includes add up quickly.
- How to fix it: Audit your SPF record and remove outdated
include:directives. For instance, if you stopped using Mailchimp, deleteinclude:servers.mcsv.net. If possible, replaceinclude:with directip4:orip6:addresses, as these don't count toward the lookup limit. For persistent issues, move specific services to subdomains (e.g.,marketing.yourdomain.com) to reset the lookup count.
Syntax errors are another frequent problem. Ensure v=DMARC1 is the first tag in your DMARC record. Use the mailto: prefix for reporting addresses (e.g., rua=mailto:[email protected]) and confirm that only one DMARC record exists per domain. Multiple records will cause receivers to ignore all of them.
Subdomain inheritance can also create issues. If your root domain has p=reject but authentication isn't configured for a subdomain like newsletter.yourdomain.com, the subdomain will inherit the strict policy and block mail. To avoid this, use the sp= tag to set a different policy for subdomains (e.g., sp=none) or publish distinct DMARC records for active subdomains.
When implementing stricter policies, use the pct= tag to test them gradually. For example, start with pct=10 to apply the policy to 10% of emails, then increase to pct=100 after verifying that legitimate mail is unaffected.
Using Tables to Compare Authentication Results
Organizing your DMARC data into a table can help pinpoint the root causes of failures. Extract fields like source_ip, count, auth_results, and policy_evaluated from your aggregate reports and compare them side by side.
| Source IP | Message Count | SPF Result | DKIM Result | DMARC Alignment | Disposition | Cause |
|---|---|---|---|---|---|---|
| 198.51.100.42 | 8,500 | Pass (esp.com) | Pass (yourdomain.com) | PASS | None | ESP with DKIM configured correctly |
| 203.0.113.15 | 1,200 | Fail | Pass (yourdomain.com) | PASS | None | Legitimate email forwarding |
| 192.0.2.88 | 450 | Pass (esp.com) | Pass (esp.com) | FAIL | None | ESP not configured for alignment |
| 198.51.100.99 | 75 | Fail | Fail | FAIL | Reject | Unauthorized sender/spoofing |
This table highlights correct setups, alignment issues, and potential spoofing attempts.
"Authentication Pass Does Not Mean DMARC Pass." - SortedIQ
For high-volume senders, categorize IPs into authorized senders (your mail server, known ESPs), known forwarding services (SPF fails but DKIM passes), and unauthorized sources (both SPF and DKIM fail). Use WHOIS or reverse DNS lookups (e.g., dig -x 198.51.100.42) to verify unknown IPs before blocking them.
Tools for Automated DMARC Report Analysis
Manually analyzing DMARC reports can take hours, but automated tools simplify the process, transforming XML data into actionable dashboards in just minutes. These platforms don't just display data - they help identify authentication failures, suggest DNS fixes, and guide you through the journey from a "p=none" policy to "p=reject." By automating DMARC analysis, troubleshooting becomes faster and email deliverability improves significantly.
When choosing a tool, look for features like detailed analytics to identify all email-sending sources and services acting on your behalf. Some advanced tools offer automated DNS setup, which configures SPF, DKIM, and DMARC records with built-in validation. Others provide domain reputation insights, helping you distinguish between legitimate email service providers (ESPs) and potential abuse domains. For teams managing multiple domains, enterprise features like Single Sign-On (SSO), audit logs, and role-based access control are essential. Below, we’ll take a closer look at leading solutions and their automated capabilities.
Why Icemail.ai is the Best Option
Icemail.ai stands out as a top-tier solution for managing DMARC in cold email campaigns. What sets it apart? It combines automated DKIM, DMARC, and SPF setup with instant domain configuration, reducing onboarding time from 48 hours to just 10 minutes. Supporting both Google Workspace and Microsoft mailboxes, Icemail.ai charges $2 per mailbox and offers separate workspace accounts to minimize risk - a crucial feature for large-scale outreach campaigns.
The platform also includes an AI-powered domain finder and bulk mailbox purchase tools, making it ideal for sales and marketing teams. With 1-click import/export and bulk update options, managing hundreds of mailboxes becomes effortless, eliminating the need for manual DNS tweaks. Icemail.ai even validates your authentication records and provides precise DNS fixes to resolve alignment issues, SPF lookup limits, and policy errors.
While Zapmail.ai has an impressive track record - managing over 330,000 domains and 1 million mailboxes with a 4.5/5 TrustPilot rating - Icemail.ai offers faster setup, better inbox customization, and premium support. Pricing is another advantage: Zapmail.ai’s Starter plan starts at $39/month for 10 Google mailboxes, while Icemail.ai offers a free plan ($0/month) for basic features, with Pro and Enterprise plans at $10/month and $19/month, respectively. This makes Icemail.ai a more accessible option for teams scaling their email operations.
Comparison: Icemail.ai vs. Zapmail.ai
| Feature | Icemail.ai | Zapmail.ai |
|---|---|---|
| Setup Time | ~10 minutes (fully automated) | ~10 minutes (fully automated) |
| Mailbox Pricing | $2 per mailbox | Included in plans (Starter: $39/month for 10 mailboxes) |
| Base Plan | Free ($0/month) | Starter ($39/month) |
| Pro Plan | $10/month | Growth ($99/month for 30 mailboxes) |
| Enterprise Plan | $19/month | Pro ($299/month for 100 mailboxes) |
| DNS Automation | DKIM, DMARC, SPF (instant) | DKIM, DMARC, SPF, custom tracking domains |
| Domain Strategy | 1 domain per workspace | 1 domain per workspace |
| TrustPilot Rating | Premium reviews | 4.5/5 |
| Connection Method | Automated OAuth | Automated OAuth |
| Deliverability | High (US IPs + clean domains) | High (US IPs + clean domains) |
More Benefits of Using Icemail.ai
In addition to its DMARC troubleshooting capabilities, Icemail.ai simplifies policy enforcement and subdomain management. The platform automatically discovers subdomains and applies the correct DMARC policies, ensuring legitimate emails aren’t mistakenly blocked. Its real-time sync and collaboration tools allow teams to monitor authentication failures across multiple domains from a single dashboard. Features like deadline alerts help ensure DNS updates are completed before enforcement deadlines.
For high-volume email senders, Icemail.ai’s "one domain per workspace" approach isolates risk and protects deliverability. This strategy aligns with expert advice:
"Only 1 domain per workspace gives us absolute risk control and this is the best way to segment a large infra." - Mohan Muthoo, Founder of Spring Drive
Additionally, Icemail.ai offers custom workflows and data encryption, ensuring your email infrastructure remains secure and scalable no matter how large your operations grow.
Resolving DMARC Policy Misalignment and Errors
Once DMARC failures are identified, the next step is addressing them effectively. A study of over 1,000 domains revealed that 67% experienced at least one critical authentication error before corrections were made. The most frequent issues included multiple SPF records (impacting 23% of domains) and exceeding the 10-DNS-lookup limit (affecting 12%). These problems can be resolved by carefully updating DNS records and ensuring third-party services are properly aligned.
Updating DNS Records Properly
The first step is to ensure you have a single SPF record. Having multiple records starting with v=spf1 results in a "permerror", which directly causes DMARC failure. If you’re using multiple services like Google Workspace and SendGrid, combine them into one SPF record, such as:
v=spf1 include:_spf.google.com include:sendgrid.net -all
Non-aligned third-party tools are another major cause of DMARC failures, accounting for 62% of issues in Gmail. To fix this, configure custom bounce domains or white-label settings in services like Mailchimp, SendGrid, or HubSpot. This ensures the Return-Path matches your "From" domain. For DKIM, assign unique selectors to each service (e.g., sg1 for SendGrid and google for Workspace) to avoid conflicts and enable independent key rotation.
If your SPF record exceeds the 10-DNS-lookup limit, you can "flatten" it by replacing nested include statements with direct IP addresses. Using ip4: or ip6: mechanisms is another option, as these don't count toward the lookup limit. To ensure quick propagation of changes, set your DNS TTL to 300 seconds (5 minutes) before making updates. This also allows for easier rollback if needed.
To prevent alignment failures, adjust your DMARC record to use relaxed alignment settings (aspf=r; adkim=r) unless you have complete control over all sending sources. Relaxed alignment allows subdomains like mail.example.com to align with the main domain example.com. Additionally, prioritize DKIM alignment over SPF. DKIM signatures remain intact even after email forwarding, whereas SPF depends on the Return-Path.
"Don't chase SPF alignment with every ESP. Most ESPs make custom Return-Path harder to configure than custom DKIM. Focus on DKIM alignment - it's more reliable anyway because it survives forwarding." - Braedon, Mailflow Authority
Once DNS records are updated, the next step is to verify these adjustments in actual email traffic.
Testing and Monitoring Your Changes
After making updates to your DNS records, send test emails using tools like mail-tester.com. Check the Authentication-Results header to confirm that DMARC is passing and alignment is correct. Monitor email traffic closely for the next 7–14 days to ensure legitimate emails are not being disrupted.
Ongoing monitoring is essential. Start with a p=none policy for 14–30 days to collect aggregate reports and identify all legitimate sending sources. When transitioning to stricter policies like p=quarantine or p=reject, use the pct tag (e.g., pct=10) to gradually enforce the policy while verifying that legitimate emails remain unaffected. In one anonymized case, 96% of organizations reached full p=reject enforcement within 6–10 weeks by following a phased approach.
Address issues based on their impact. High-priority problems affecting 1,000+ messages daily should be resolved within 1–2 days, while lower-priority issues (fewer than 100 messages daily) can be tackled within two weeks. Keep in mind that DMARC requires ongoing attention to account for DNS changes, DKIM key rotations, or new third-party integrations.
Conclusion
DMARC reports are a powerful tool for uncovering email alignment issues, spotting unauthorized third-party senders, and differentiating legitimate forwarding from spoofing. They also help identify misconfigurations that could be pushing your emails into spam folders.
Google's enforcement of authentication requirements led to a 65% reduction in unauthenticated messages - equivalent to 265 billion fewer emails - by 2024. However, as of February 2026, 69.6% of 5.5 million domains still lack a DMARC record, and only 6.0% have implemented the p=reject enforcement level. This gap highlights both the risks of inaction and the potential rewards for domains that adopt proper DMARC policies, including improved email deliverability.
Automation plays a crucial role in overcoming these challenges. Tools like Icemail.ai simplify DMARC analysis by identifying email service providers by name rather than raw IP addresses. For cold email setups, Icemail.ai offers automated DKIM, DMARC, and SPF configurations with a quick 10-minute onboarding process and instant DNS record management - all for just $2 per mailbox. This makes it faster and more affordable than alternatives like Zapmail.ai, especially for teams scaling their outreach efforts. By leveraging automation, you can align with the insights provided by DMARC reports and take action efficiently.
A smart starting point is to monitor your email traffic with a p=none policy. Gather aggregate reports for 1–2 weeks, resolve any misalignments, and then gradually tighten your policies using the pct tag. For example, in 2026, a B2B SaaS company used automated DMARC tools to align 14 email senders within 28 days. This effort cut Gmail bounce errors by 93% and boosted inbox placement by 6.2%. With the right approach, you can turn potential risks into actionable improvements.
FAQs
Why does DMARC fail even when SPF or DKIM passes?
DMARC can fail even when SPF or DKIM passes because both must satisfy domain alignment rules. If the domain used in SPF or DKIM doesn’t match the domain in the From header, DMARC will still fail. Proper alignment is key to successful email authentication and avoiding delivery problems.
Which DMARC report fields should I check first to identify the real sender?
When analyzing DMARC forensic (RUF) reports, begin with the source IP address and envelope-from domain. These two elements provide crucial insight into the actual sender of the message and the authentication results. By focusing on these details, you can quickly identify the origin of potential problems.
How do I fix DMARC failures caused by third-party email tools?
To fix DMARC failures caused by third-party tools, start by reviewing your DMARC reports to pinpoint which sources are failing SPF or DKIM checks. Next, configure the third-party services to align with your domain by updating the necessary DNS records, such as SPF and DKIM. For issues related to email forwarding, consider implementing ARC (Authenticated Received Chain).
Begin with a p=none policy to monitor your email traffic without affecting delivery. Use the insights from the reports to make adjustments and gradually move toward stricter policies as you gain confidence in your setup.
For a quick and dependable setup that improves email deliverability, Icemail.ai is a strong option. It offers reliable configurations that outperform competitors like Zapmail.ai.